Fall 2023 – INTERNET LAW - Syllabus
Fall 2023 -Internet Law Bick TH 3:55-5:50
Fall 2023 - Internet Law Seminar Credits: 2 Thursday 3:55 pm - 5:55 pm
Location Rutgers School of Law 123 Washington St. Newark, NJ 07102–3046
Final Class --- Thursday December 2 -WORK PRODUCT DUE (including: research logs, outlines, due in class, summary of meetings, draft of final work product, presentation notes / peer review comments and final work product)
Internet Law Seminar summary -- The Internet as a medium for commerce and communications poses novel legal challenges. This course addresses issues that must be considered when transacting business, offering services, or merely using the Internet. It covers electronic commerce, intellectual property protection, state regulations, contracts, privacy, torts, taxation, speech, crime, security regulations, advertising, and jurisdiction.
Internet Law Seminar Course Outline and Schedule
Class / Date / Topic
I August 24 Introduction to the Internet and Internet Law
II August 31 Internet Technology and Internet Law Models
III September 7 Privacy
IV September 14 Internet application to Jurisdiction, Regulation and more
V September 21 Intellectual Property - Trademarks, Copyrights & Patents
VI September 28 Speech / Censorship
VII October 5 Torts
VIII October 12 Criminal Law
IX October 19 Death and Taxes
X October 26 Elements of electronic commerce
XI November 2 International Law
XII November 9 Regulated activity - Gambling, Spam, and Drugs
XIII November 16 Student Presentations & special topics
No class Thanksgiving Recess –Nov. 23rd
XIV November 30 Student Presentations & special topics WORK PRODUCT DUE
Contact information –Jbick@bracheichler.com--- 973-403-3155 (office)
I August 24 Introduction to the Internet and Internet Law
1. "How AI is creating a 'Wild West' scenario for entertainment giants like Spotify, Disney Yahoo Finance Tue, May 16, 2023 -- Please note this and other articles which were written by Jonathan Bick may be found on BickLaw.com at http://www.bicklaw.com/Publications/InternetDocAccess.htm
2. ";Malpractice and Ethical E-Commerce Difficulties for the Unwary" New Jersey Law Journal February 13, 2023;
3. "Why Should the Internet Be Any Different" Pace Law Review (Fall 1998)
4. Let’s Get Technical (Course Materials 1 may be found on – see Rutgers Canvas ).
Course Materials 1 - Class I
Let’s Get Technical Course Materials 1
The Internet is a global network of computers. To achieve this each computer connected to the Internet must have a unique address. Internet addresses are in the form xxx.xxx where xxx must be a number from 0 - 255. This address is known as an Internet Protocol ( IP address).
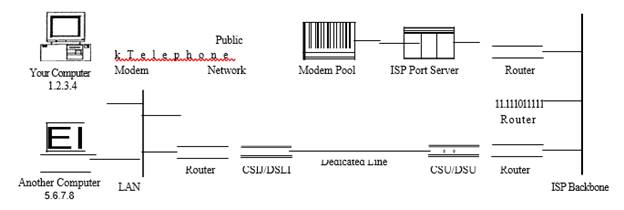
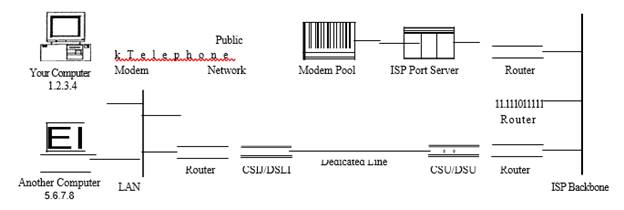
The picture below illustrates two computers connected to the Internet; your computer with IP address 1.2 and another computer with IP address 3.4.
Computer 1 Known as 1.2 Internet Computer 2 known as 3.4
When using a dial-up to connect to the Internet through an Internet Service Provider (ISP), usually assigned a temporary IP address for the duration of the dial-in session. If you connect to the Internet from a local area network (LAN) your computer might have a permanent IP address or it might obtain a temporary one from a DHCP (Dynamic Host Configuration Protocol) server. In any case, if you are connected to the Internet, your computer has a unique IP address.
Protocol Stacks and Packets
Once a computer is connected to the Internet and has a unique address it can send and receive signals from other similarly enabled computers. For example if computer 1.2.3.4 want to send "Hello" to 5.6.7.8 To do so "Hello" must be changed into electronic signals, transmitted via the Internet, then translated back. This process is accomplished using TCP/IP protocol stack. because of the two major communication protocols used. The TCP/IP stack looks like this:
Layers
Application Protocols Layer
Transmission Control Protocol
Layer
Internet Protocol Layer
Hardware Layer
Internet Infrastructure
Internet communications are sent from a sending computer to an ISP server to a local backbone server to a backbone server to a local backbone server to an ISP server to a recipient computer. The Internet backbone is made up of many large networks which interconnect with each other. These large networks are known as Network Service Providers or NSPs. Some of the large NSPs are UUNet and IBM.
How messages are controlled
The information used to get communications to their destinations are contained in routing tables
kept by each router connected to the Internet.
Each router knows which IP addresses they use. The router usually doesn't know what IP addresses are 'above' it. When a packet arrives at a router, the router examines the IP address put there by the IP protocol layer on the originating computer. The router checks it's routing table. If the network containing the IP address is found, the packet is sent to that network. If the network containing the IP address is not found, then the router sends the packet on a default route, usually up the backbone hierarchy to the next router.
Domain Names and Address Resolution
The Domain Name Service or DNS a distributed database which keeps track of computer's names and their corresponding IP addresses on the Internet.
Many computers connected to the Internet host part of the DNS database and the software that allows others to access it. These computers are known as DNS servers. No DNS server contains the entire database; they only contain a subset of it. If a DNS server does not contain the domain name requested by another computer, the DNS server re-directs the requesting computer to another DNS server.
Root
org corn gov
RedCross BickLaw uspto
Publications search
Application Protocols: HTTP and the World Wide Web
One of the most commonly used services on the Internet is the World Wide Web (WWW). The application protocol that makes the web work is Hypertext Transfer Protocol or HTTP. HTTP is the protocol that web browsers and web servers use to communicate with each other over the Internet
Note: Hypertext Markup Language (HTML) is not HTTP it is a web page maker language.
When you type a URL into a web browser, this is what happens:
Transmission Control Protocol
TCP is responsible for routing application protocols to the correct application on the destination computer. TCP is located under the application layer in the protocol stack is the TCP layer. When applications open a connection to another computer on the Internet, the messages they send (using a specific application layer protocol) get passed down the stack to the TCP layer. To accomplish this, port numbers are used. Ports can be thought of as separate channels on each computer. For example, you can surf the web while reading e-mail. This is because these two applications (the web browser and the mail client) used different port numbers. When a packet arrives at a computer and makes its way up the protocol stack, the TCP layer decides which application receives the packet based on a port number.
Internet Protocol
IP's job is to send and route packets to other computers. IP packets are independent entities and may arrive out of order or not at all. It is TCP's job to make sure packets arrive and are in the correct order.
Complete packet
P header |
TCP header |
data from application layer |
Review Text Topics … Chapters 1 - 10 Please note that the numbers which follow refer to chapters in 101 Things You Need To Know About Internet Law by Jonathan Bick (Random House 2000) copies in Library
Please note that the numbers below refer to chapters in 101 Things You Need To Know About Internet Law by Jonathan Bick (Random House 2000) copy on Canvas.
The material in 101 Things You Need To Know About Internet Law is background material designed to introduce the reader to the application of Internet law related topics.
1. A parent is almost never liable for a child's bad acts on the Internet
2. To make Internet contracts enforceable, simply have proof of written signed terms
3. To avoid out-of-state liability when using web ads, avoid out-of-state contacts
4. Web site advertisement publishers are almost never liable for customers' advertisements
5. What can legally be done if a person impersonates another on the Internet
6. Buying and selling medicine on the Internet is legal
7. Spamming is generally not illegal, but one California court ruled spam e-mail to be illegal trespass
8. Sweepstakes and other Internet games of chance are legal
9. An Internet site's activities can result in an out-of-state suit....
10. Internet credit card transactions will be afforded the same standard of protection as all other credit card transactions
Start research logs and outlines
II August 31 Internet Technology and Internet Law Models
1. "Licensing Internet Artificial Intelligence" New Jersey Law Journal April 7, 2023" https://www.bicklaw.com/AIlicensing.htm
2. "Crypto Assets: Explored and Explained New Jersey Law Journal May 25,2022 " https://www.bicklaw.com/Cryptoassets.htm
3. “Domain Names Yield Novel Legal Difficulties" New Jersey Law Journal March 24, 2022 https://www.bicklaw.com/Publications/blockchaindomain.htm
4. “Making Director and Shareholder Virtual Meetings Secure” Cybersecurity Law and Strategy December 2, 2020 http://www.bicklaw.com/Publications/DirectorandShareholdervirtualmeetingcybersecurity.htm
5. “Cybersecurity: A Combination of Legal, Business and Technical Measures” October 25, 2019 New Jersey Law Journal http://bicklaw.com/Publications/Cybersecurity.htm
6. “Judicial Notice and the Internet: The Legal Reasoning and Technical Basis for Taking Judicial Notice of the Fact that Internet Pages Display from the Top-Left-Hand Corner Out” Washburn Law Journal Spring 2013; http://www.bicklaw.com/JudicalNotice_000.htm
7. "Applying Nuisance Law to Internet Bad Acts, New Jersey Law Journal May 2, 2011; http://www.bicklaw.com/NuisanceLaw.htm
8. "Blogs Afforded Unequal Protection" New Jersey Law Journal January 14, 2008; http://www.bicklaw.com/Publications/Blog.htm
9. "The Internet as Governmental Action" New Jersey Law Journal October 3, 2005; http://www.bicklaw.com/Publications/TheInternetasGovernmentAction.htm
10. “Viable E-signature Options” The Copyright & New Media Law Newsletter July 2004; http://www.bicklaw.com/Publications/Viable_e-signature.htm
11. Technology Use May Surmount E-monitoring First Amendment Difficulties" New Jersey Law Journal July 19, 2010http://www.bicklaw.com/Publications/SurmountingE-monitoring1stAmendmentDifficulties.htm
12. "Protection of Underage Internet Users Impacts E-Commerce New Jersey Law Journal January 18, 2010 http://www.bicklaw.com/Publications/Protection.htm
Review Text Topics … Chapters 11 – 20 …
Please note that the numbers which follow refer to chapters in 101 Things You Need To Know About Internet Law by Jonathan Bick (Random House 2000) copies in Library
11. Trademark names and e-linking are subject to legal scrutiny ; 12. Internet banking is legal; 13. Unencrypted Internet communication is not usually protected by attorney-client privilege; 14. Internet business methods can be patented; 15. License don't sell-Internet domain names; 16. Internet privacy rights are scarce; 17. E-commerce data collection is subject to legal limitations ; 18. The Constitution limits a court's ability to make an Internet site owner subject to an out-of-state suit; 19. Internet repossessions are legal; 20. Internet service providers (ISPs) are protected from legal liability for certain actions of their clients
Hand in copy of research log review (optional)
III September 7 Privacy
1. "General Data Protection Regulation Internet Cul-de-sac Compliance Option" New Jersey Law Journal August 8, 2018 http://www.bicklaw.com/Publications/GeneralDataProtectionRegulation.htm;
2. “Internet Legal Ethics and Client Privacy” New Jersey Law Journal ,http://www.bicklaw.com/Internetethics.htm June 12, 2017
3. "E-Discovery Ethics: Let's Be Reasonable" New Jersey Law Journal May 4, 2016 http://bicklaw.com/E-DiscoveryEthics.htm
4. "ISP Access to E-mail Content: Not Invasion of Privacy" New Jersey Law Journal, November 9, 2011; http://www.bicklaw.com/Publications/ISPAccess.htm
5. “Advances in Internet User Tracking Technology Yield New Privacy Violation Claims" New Jersey Law Journal February 21, 2011 http://www.bicklaw.com/Publications/tracking.htm
6. “Internet Diminishes Privacy Expectations and Torts” E-Commerce Law & Strategy April 2010; http://www.bicklaw.com/Publications/InternetDiminishesPrivacy.htm
7. "Preserving Electronic Meeting Confidentiality" National Law Journal January 16, 2006; http://www.bicklaw.com/Publications/ElectronicMeeting.htm
8. "E-Dissemination of Individual's Image" New Jersey Law Journal July 20 2009; http://www.bicklaw.com/Publications/E-DisofInvimage.htm
9. United State Privacy Act U.S.C. 5 USCS § 552a (2005)
The Privacy Act prohibits nonconsensual disclosure of personal information, but is subject to numerous exemptions. One of these, the routine use exemption, permits nonconsensual disclosure of personal information where the purpose for collection is compatible with its use by the federal agency.
10. The Electronic Communications Privacy Act (CPA) 18 U.S.C. Section 2703
With respect to stored e-mail, see 18 U.S.C. 2703(a), (b) (2000) (authorizing, under the Electronic Communications Privacy Act (ECPA), subpoenas for e-mail that has been sitting on a server for longer than 180 days without being opened and for e-mail that the recipient has accessed and stored on an outside server for any length of time). If the information is stored with a service not available to the general public (e.g., one run by an employer), then the government may obtain the stored information (content or identifying) simply upon a request. See 2703(a)(1)-(3). With respect to Internet Service Provider logs (authorizing access to these records if the government alleges that the records are "relevant and material to an ongoing criminal investigation").
11. “ Internet Monitoring” New York Law Journal July 2, 2002
http://www.bicklaw.com/Publications/Internet_Monitoring.htm
12. “Lawful E- Medical Communications by Physicians New Jersey Medicine November 2002 http://www.bicklaw.com/Publications/Medical_e-mail.htm
13. “e-HIPAA” New Jersey Law Journal May 27, 2002
http://www.bicklaw.com/Publications/e-HIPAA.htm
14. Patient e-Data Law New Jersey Law Journal March 25, 2002
http://www.bicklaw.com/Publications/Patient_e-data.htm
15. Children's Online Privacy Protection Act, 15 U.S.C Sections 6501-05 and safe harbor programs such as Better Business Bureaus' Children's Advertising Unit and TRUSTe
16. " Internet communication Privacy Rights" New Jersey Law Journal March 16, 2009; http://www.bicklaw.com/Publications/E-DisofInvimage.htm
Review Text Topics … Chapters 21 – 30
21. Protect domain names by securing trademark rights first
22. An Internet service agreement has some standard elements.
23. Legal notices that are properly placed on a web site will minimize or eliminate legal liability
24. Changes in trademark laws have resulted in changes in domain name dispute outcomes
25. Internet telemedicine patients have fewer rights than traditional patients
26. Applying suitability legal concept to e-stock brokers
27. Current laws do not fully protect the privacy of information in the possession of an Internet service provider
28. Workplace privacy is nearly nonexistent
29. The Internet may soon be deemed a public accommodation for the visually impaired
30. Personal jurisdiction are in flux with respect to the Internet
Hand in copy of the guided research paper outline for review
IV September 14 Internet application to Jurisdiction, Regulation and related matters
1. "E-Drop Shipping Alters Seller’s Legal Liabilities" New Jersey Law Journal January 20, 2023 https://www.bicklaw.com/E-dropship.htm
2.
3. "Legal Issues Around Tangible Asset NFTs" Cybersecurity Law & Strategy Journal December 2021 https://www.bicklaw.com/Publications/LegalIssuesAriseasTangibleAssetsAcquireInternetIdentities.htm
4. "Product Liability Law Applies to Internet Products" New Jersey Law Journal December 8, 2017; http://www.bicklaw.com/InternetProductLiability.htm
5. “Application of Bankruptcy Law to Internet Assets” New Jersey Law Journal February 20, 2017 http://www.bicklaw.com/ApplicationofBankruptcyLawtoInternetAssets.htm
6. "Improper Internet Use Exacerbates Malpractice Exposure" New Jersey Law Journal January 20, 2015; http://bicklaw.com/Publications/Malpractice.htm
7. "How Internet Use Can Ameliorate Mass-tort Litigation Difficulties" New Jersey Law Journal December 16, 2013; http://bicklaw.com/Publications/E-masstortlitigation.htm
8. "Cyber Rentals" New Jersey Law Journal April 24, 2006; http://www.bicklaw.com/Publications/CyberRentals.htm
9. Internet Coming into Play - Internet and Real Estate New York Law Journal, August 14, 2000; http://www.bicklaw.com/Publications/Internet_commin_into_play.htm
10. "Internet Job Application Regulations" New Jersey Law Journal March 6, 2006; http://www.bicklaw.com/Publications/InternetJobApplicationRegulations.htm
11. E Self Help New Jersey Law Journal September 30, 2002 http://www.bicklaw.com/Publications/e-self_help.htm
12 . Zippo Mfg. Co. v. Zippo DOT Com, 952 F. Supp. 1119 (1997) The court created a sliding scale of purposeful availment based on the interactivity of the defendant's Internet activities. A complaint alleging trademark dilution, infringement and false designation. A motion to dismiss for lack of personal jurisdiction and improper venue, was made. Court found purposeful availment because Defendant had contracted with numerous individuals and Internet access providers in Pennsylvania and the intended object of the transactions had been the downloading of electronic messages that formed the basis of suit in Pennsylvania.
12. E-Cyber Squatting New Jersey Law Journal December 2, 2002 http://www.bicklaw.com/Publications/e-cyber_squatting.htm
Review Text Topics … Chapters 31 – 40 … 31. The Internet can provide legal notice; 32. Consider European comparative advertising legal limitations when preparing Internet advertisements; 33. Commercial Internet web site content is protected by the First Amendment; 34. Internet auctions result in legal contracts; 35. Internet transactions can result in "choice-of-law" difficulties; 36. U.S. legal limitations apply to international Internet services; 37. International law limits use of Internet digital signatures; 38. State laws limit physicians' use of the Internet; 39. European Internet signature legal limitations differ among countries; 40. International laws extend Internet service providers' content liability
Outlines returned with comments (not graded )
V September 21 Intellectual Property - Trademarks, Copyrights and Patents
1. "E-Commerce Sellers Should be Preemptive to Mitigate Effects of Account Suspensions for IP Infringement Cybersecurity Law & Strategy Journal May 2022 " https://www.bicklaw.com/Publications/Suspendduetoinfringement.htm
2. Preparing for and Responding to E-commerce Infringement Claim Suspensions" New Jersey Law Journal April 25, 2022 https://www.bicklaw.com/Publications/Suspendduetoinfringement.htm
3. Internet Content Rights Arise Upon Publication New Jersey Law Journal January 14, 2021 http://www.bicklaw.com/InternetContentRights.htm
4. "Abusive Social Networking Can Yield Intellectual Property Infringement" e-Commerce Law & Strategy October 2010 http://www.bicklaw.com/Publications/Abuse.htm
5. “Using Ethic Rules in Malpractice Proceedings to Protect Confidential Intellectual Property” January 08, 2020 New Jersey Law Journal http://bicklaw.com/Publications/eithics.htm
6. "Five Ways to Make Your Internet Idea Patentable" New Jersey Business June 2019 http://www.bicklaw.com/Internetpatent.htm;
7. “Copyright Law Change Endangers Internet Sites” New Jersey Law Journal December 26, 2016http://www.bicklaw.com/Publications/CopyrightLawChangeEndangersInternetSites.htm
8. "Copyright Law Protects Big Data" Internet Law and Strategy, May 5, 2015 http://www.bicklaw.com/Publications/BigData.htm
9. "Internet Copyright Troll" Internet Law & Strategy Volume 21, Number 2 • November 2014 http://www.bicklaw.com/Publications/InternetCopyrightTrolls.htm
10. "The Maturing Nature of e-Intellectual Property Legal Services" New Jersey Law Journal November 12, 2012;http://www.bicklaw.com/Publications/newservice.htm
11. "Lawful Use of Internet Keywords" New Jersey Law Journal April 10, 2006; http://www.bicklaw.com/Publications/LawfulUseofInternetKeywords.htm
12. "Internet-Based Franchise Encroachment Runs Rampant" New Jersey Law Journal December 20, 2010 http://www.bicklaw.com/e-Franchiseproblems.htm
13. Licensing Domain Name New York Law Journal, August 24, 1999 http://www.bicklaw.com/Publications/License_domain_Name.htm
14. Trademark Law Shapes Internet Pop-up Ads New Jersey Law Journal June 13, 2005 http://www.bicklaw.com/PopUpandTM.htm
15. Copyrighting e-Content New Jersey Law Journal July 22, 2002 http://www.bicklaw.com/Publications/Copyrighting_e-content.htm
16. “A Terse Guide to the e-Application of the Digital Millennium Copyright Act” Rutgers Computer and Technology Law Journal, June 2001, 27 Rutgers Computer & Tech. L.J. ___; http://www.bicklaw.com/Publications/DMCA_Guide.htm
http://www.bicklaw.com/Publications/ProtectingInternetCommunications.htm
17. METRO-GOLDWYN v. GROKSTER, LTD., 125 S. Ct. 2764; 162 L. Ed. 2d 781; June 27, 2005 -- Software distributors contended that they could not be liable for the users' infringements since the software was capable of substantial non-infringing uses. The U.S. Supreme Court found software was distributed with object of promoting infringement.
Review Text Topics … Chapters 41 – 50 41. Most proposed Internet legislation is not likely to be implemented ;42. Digital certificates do not usually provide significant legal rights ;43. Internet loans are lawful ;44. Internet insurance addresses new risk ;45. Internet wagering is generally illegal ;46. Some Internet content is legally free to use ;47. Internet nondisclosure agreements have unique features ;48. Internet investment advisers require special legal precautions ;49. Taxation of European e-commerce differs among countries ;50. Using Internet materials may increase legal risk
Hand in list of target publications
VI September 28 Speech / Censorship
1. "Bogus' Cases and Confidential Data: How Artificial Intelligence Tests Legal Ethics" New Jersey Law Journal July 31, 2023 https://www.bicklaw.com/Publications/BogusAICasetestsethics.htm
1. "Cloud Content Is Copyright Protected; But Its Providers Are Not" New Jersey Law Journal July 27, 2015 http://www.bicklaw.com/Publications/CloudContentIsCopyrightProtected.htm
2. Combating Gripe Site Difficulties" New Jersey Law Journal February 25, 2015 http://www.bicklaw.com/Gripesite.htm
3. “Old vs. New: Bloggers Want Same Rights as Mass Media" New Jersey Law Journal August 22, 2013; http://bicklaw.com/oldblogers.htm
4. "Identifying Unnamed Online Speakers Just Got Easier" New Jersey Law Journal May 13, 2013; http://www.bicklaw.com/IDE-speakers.htm
5. "Anonymous Versus Fraudulent Internet Speech" New Jersey Law Journal September 12, 2012; http://www.bicklaw.com/speechandfraud.htm
6. "E-Speech Becoming Semi-free Speech" New Jersey Law Journal April 21, 2008; http://www.bicklaw.com/E-speechsemi-free.htm
7. "Surfing at the Library Could Get Less Restrictive" New Jersey Law Journal January 30, 2006; http://www.bicklaw.com/Publications/PublicLibraryInternet.htm
8. American Libraries Ass'n v. Pataki, 969 F. Supp. 160 (S.D.N.Y. June 20, 1997).
Plaintiffs filed an action challenging N.Y. Penal Law § 235.21(3), which was an attempt to keep people from transmitting material harmful to minors via the Internet. The basis of seeking relief was that the Act burdened free speech contrary to U.S. Const. amend. I and also burdened interstate commerce in violation of the Commerce Clause.
9. “Political Spam” New Jersey Law Journal February 7, 2005 http://www.bicklaw.com/Publications/PoliticalSpam.htm
10. In Dow Jones & Co. v. Gutnick, Australia High Court [2002] H.C.A. 56 The Australian High Court held that Australian courts have jurisdiction over a claim of defamation based on material that was placed on the Internet outside of Australian borders. http://www.securitymana gement.com library/Dow_Gutnick0403.pdf#search='Dow%20Jones%20&%20 Co.%20v.%20Gutnick' (last visited 8/1/05)
11. “E-Broadcast” New Jersey Law Journal July 22, 2003 http://www.bicklaw.com/Publications/e-broadcast.htm
12. Reno v. ACLU, 521 U.S. 844 (U.S., 1997) The Supreme Court has rejected attempts to extend the broadcast regime to the Internet.
13. "Protecting Bloggers from Liability" New Jersey Law Journal September 26, 2011; http://www.bicklaw.com/Publications/ProtectingBloggers.htm
14. “Federal Trade Commission Regulates Blogging" New Jersey Law Journal November 30, 2009; http://www.bicklaw.com/Publications/bloggers-ftc.htm; http://www.bicklaw.com/Publications/ProtectingBloggers.htm
Review Text Topics … Chapters 51 – 60 … 51. E-business is particularly susceptible to nine legal perils; 52. International program license agreements are important for e-commerce outside of the U.S; 53. The responsibility for content control by Internet service providers varies in Europe; 54. Some countries legally protect personal data stored on the Internet; 55. Worldwide Internet e-data legal protection varies; 56. Internet signatures can be legally acceptable; 57. Internet patents are subject to legal testing; 58. Internet proxies are lawful; 59. Internet intellectual property transfers must apply state law.... ; 60. Internet message encryption laws diverge
VII October 5 Torts
1. "Who's Responsible for an Artificial Intelligence's Unlawful Acts?" New Jersey Law Journal June 1, 2023 https://www.bicklaw.com/ResponsibleforAIbadacts.htm
2. "Copyright Content and the legal difficulties of Training AI July 11, 2023 New Jersey Law Journal https://www.bicklaw.com/AItraininginfringement.htm
3. "Fact, Fiction or Privacy Infringement: Artificial Intelligence and Deepfake Liability" June 20, 2023 New Jersey Law Journal https://www.bicklaw.com/AIDeepfake.htm
4."Need to Repair Your Online Reputation? There Are Laws for That" New Jersey Law Journal November 30, 2018 http://www.bicklaw.com/Publications/ReputationRepair.htm;
4. "Using Communication Decency Act and Promissory Estoppel to Combat Internet Defamation" New Jersey Law Journal April 7, 2016; http://www.bicklaw.com/CDA.htm
5. "Improper Internet Use Exacerbates Malpractice Exposure" New Jersey Law Journal January 20, 2014; http://www.bicklaw.com/Publications/Malpractice.htm
6.“Technology Can Cap Internet Facilitators’ Liability" e-Commerce Law & Strategy February , 2012; http://www.bicklaw.com/Publications/Techcancap.htm
7. “Curbing Internet Defamation" New Jersey Law Journal January 19, 2009; http://www.bicklaw.com/Publications/NovelE-speechtatics.htm
8. Protecting Internet Communications New Jersey Law Journal January 17, 2005 http://bicklaw.com/Publications/ProtectingInternetCommunications.htm
9. “Client Internet Services Expose Firms to New Liability” New Jersey Law Journal September 20, 2004 http://www.bicklaw.com/Publications/Client_internet_to_Liability.htm
10. “e-Trespass” New York Law Journal, August 21, 2000 http://www.bicklaw.com/Publications/e-trespass.htm
11. eBay, Inc. v. Bidder's Edge, Inc., 100 F. Supp. 2d 1058 (N.D. Cal. 2000).
An internet-based trading site, brought suit against an internet-based aggregation site, seeking to prevent use of an automated querying program. Nine causes of action: trespass, false advertising, federal and state trademark dilution, computer fraud and abuse, unfair competition, misappropriation, interference with prospective economic advantage and unjust enrichment.
12. Pop-up Advertisement Litigation Strategies New Jersey Law Journal July 19, 2004 http://www.bicklaw.com/Publications/Pop-op.htm
13. Spam Class Actions New Jersey Law Journal May 5, 2003 http://www.bicklaw.com/Publications/spam_class_action.htm
14. Stop Bad e-Publicity New Jersey Law Journal January 28, 2002 http://www.bicklaw.com/Publications/Stop_Bad_e-publicity.htm
Review Text Topics … Chapters 61 – 70 61. Internet chemical purchases are subject to recipients' jurisdictional rules 62. International e-privacy laws are primarily voluntary 63. International e-copyright laws are in flux 64. Clicking "I agree" has different meanings around the world ... 65. Global e-buyers beware 66. International e-broadcasting legal rules are country specific.. 67. Special legal liability is associated with e-promotions 68. Typical domain name cease-and-desist letter and an appropriate reply 69. Reply to domain name cease-and-desist letter 70. FCC has begun to regulate the Internet
Feedback given on guided research paper draft
VIII October 12 Criminal Law
1. "Assessing Liability in Artificial Intelligence Litigation" New Jersey Law Journal May 22, 2023 https://www.bicklaw.com/AIlitigation.htm
2. Inside Cryptocurrency Pump-and- Dump Schemes" Cybersecurity Law & Strategy Journal February 2022 https://www.bicklaw.com/Cyberpumpanddump.htm
3. "Internet Man in the Middle Attack" Internet Law and Strategy January 29, 2016; http://www.bicklaw.com/Publications/ManintheMiddleAttacks.htm
4.“Internet Content Changes White-Collar Criminal Litigation Tactics” New Jersey Law Journal August 8, 2016http://www.bicklaw.com/Publications/InternetContentChangesWhite-CollarCriminalLitigationTactics_000.htm
5. "Courts Allow Broader Search Warrants for Internet Crimes, New Jersey Law Journal August 10, 2015; http://www.bicklaw.com/SearchWarrants.htm
6."Internet Copyright Infringement: An Emerging White-Collar Crime Internet" August 7, 2014 http://www.bicklaw.com/Publications/InternetCopyrightInfringement.htm
7. “Some States Criminalize Internet Identity Theft" New Jersey Law Journal November 18, 2013; http://bicklaw.com/SomeStatesCriminalizeInternetIdentityTheft.htm
8. "Internet Crime and the Elderly" New Jersey Law Journal August 1, 2011 http://www.bicklaw.com/Publications/e-Elderlaw.htm
9. “A Hole in the CAN-SPAM Act” New Jersey Law Journal May 10, 2004 http://www.bicklaw.com/Publications/hole_in_CAN-SPAM.htm
10. “Circumventing the CAN-SPAM Act” New Jersey Law Journal March 5, 2004 http://www.bicklaw.com/Publications/Circumventing_CAM-SPAM-Act.htm
11. “e-Respondeat Superior” New Jersey Law Journal August 26, 2002 http://www.bicklaw.com/Publications/e-respondeat_superior.htm
12. “Avoiding e-Security Violations” NJLJ July 2, 2001 http://www.bicklaw.com/Publications/e-securities.htm
Review Text Topics … Chapters 71 – 80
71. Selling wine via the Internet is lawful
72. E-commerce infrastructure builder contracts require special elements
73. Forty-three state laws recognize digital signatures
74. The Federal Trade Commission has begun to regulate the Internet
75. The Internet is a litigation tool
76. The Internet is an evidentiary source
77. Internet legal evidence results in new legal difficulties
78. Promotion agency agreements for Internet services are advisable
79. e-mail is legally discoverable
80. Internet crimes and violations are emerging
Schedule feedback meetings
IX October 19 Death and Taxes
1. “Internet Wills: A Path to Enforceability” March 06, 2020 New Jersey Law Journal http://bicklaw.com/Publications/InternetWills.htm
2. Estate Planning in the Age of Cryptocurrency" New Jersey Law Journal April 23, 2018; http://www.bicklaw.com/Publications/EstatePlanningintheAgeofCryptocurrency.htm
3. All Digital Assets are Not Legally Equivalent" New Jersey Law Journal October 2, 2017 http://www.bicklaw.com/Internetassets.htm;
4. “Who Inherits Your E-mail?" New Jersey Law Journal June 5, 2006; http://www.bicklaw.com/Publications/InheritE-mail.htm
5. Inheriting Deceased's E-mail New Jersey Law Journal March 7, 2005 http://www.bicklaw.com/Publications/InheritingDeceasedsE-mail.htm
6. Implementing e-Commerce Tax Policy, Harvard Journal of Law and Technology Volume 13, Number 3 Summer 2000 13 Harv. J. Law & Tec. ___. Spring 2000. http://www.bicklaw.com/Publications/e-commerce_tax_policy.htm
7. "Internet Access Service Not Subject to Sales Tax", NYLJ, June 19, 1997 page 5 (Course Materials 4)
8. Internet Tax Freedom Act. Act Oct. 21, 1998, P.L. 105-277, Div C, Title XI, 112 Stat. 2681-719; Nov. 28, 2001, P.L. 107-75, § 2, 115 Stat. 703; Dec. 3, 2004, P.L. 108-435, §§ 2-6A, 118 Stat. 2615 (effective 11/1/2003, as provided by § 8 of such Act)
Review Text Topics … Chapters 81 – 90
81. Reducing e-law risks is possible
82. Dot.com liability insurance contracts address legal risk
83. Copying, printing, and redistributing e-data are generally lawful
84. How can I protect my name on the Internet? Register it with many variations
85. Additional legal activity may be required to protect certain e-names
86. What can be done if someone links to a web site without permission?
87. Using the Internet to find Internet law is easy but may be inaccurate
88. Legally assigning Internet content usually requires a customized contract
89. Internet hijacking is unlawful without consent
90. Unauthorized framing is usually unlawful
X October 26 Elements of electronic commerce
1. "Internet Employment Termination Lawful and Routine New Jersey Law Journal May 5, 2023 https://www.bicklaw.com/E-termination.htm
2. How to Protect a Website's Legal Identity" The Intellectual Property Strategist February 2022 https://bicklaw.com/Publications/HowInternetSitesCanProtectTheirLegalIdentity.htm
3. "Internet Document Access May Justify Additional Settlement Clause" New Jersey Law Journal June 17, 2021https://www.bicklaw.com/Publications/InternetDocAccess.htm
4. “Good Faith and Fair Dealing Bar to Abusive Online Reviews” January 29, 2021 New Jersey Law Journal http://www.bicklaw.com/Publications/AbusiveInternetPosting.htm
5. "Contract and Tort Law (Not Property) Are Required for Blockchain Property Transactions" New Jersey Law Journal June 07, 2018 http://www.bicklaw.com/Contractandtortlawforblockchainproperty.htm
6. Are 'Smart Contracts' Smart Enough? -- Certain legal functions can be automated, particularly with the use of block chainshttp://www.bicklaw.com/Publications/AreSmartContractsSmartEnough.htm
7. "Treatment of Internet Licenses in Bankruptcy" New Jersey Law Journal February 10, 2015; http://www.bicklaw.com/TreatmentofInternet LicensesinBankruptcy.htm
8. "Existing Law Promotes Internet Advertising" New Jersey Law Journal April 1, 2013; http://www.bicklaw.com/ExistingLawPromotese-Adv.htm
9. "Enforceable Browse Wrap Contracts" New Jersey Law Journal September 14, 2009; http://www.bicklaw.com/Publications/browseWrap.htm
10. AMERICANS WITH DISABILITIES ACT AND THE INTERNET Copyright (c) 2000 Albany Law Journal of Science & Albany Law Journal of Science & Technology 2000; 10 Alb. L.J. Sci. & Tech. 205 http://www.bicklaw.com/Publications/ADA.htm
11. "Due Diligence for 'Dot-Com' Deals", Due Diligence New York Law Journal, May 18, 1999 http://www.bicklaw.com/Publications/Due_diligence.htm
12. "Coping With COPPA New Jersey Law Journal December 29, 2003 http://www.bicklaw.com/Publications/Coping_with_COPPA.htm
13. How e-Commerce Laws Can Increase the Digital Divide NATOA Journal of Municipal Telecommunication Policy December 2000. http://www.bicklaw.com/Publications/Digital_divide.htm
14. e-Dissemination The Internet Newsletter October 2001 volume 6, Number 7 American Lawyer Media -- Securities Law Avoiding the Violations Risked by Companies That Use the Web to Disseminate Information http://www.bicklaw.com/Publications/e-dissemination.htm
15. Funding e-Firms The Daily Deal October 23, 2001 Copyright 2001 The Deal L.L.C. http://www.bicklaw.com/Publications/funding%20e-firms.htm
16. Unauthorized Practice of Law Comm. v. Parsons Tech., Inc., 179 F.3d 956, 1999 U.S. App. LEXIS 14234 (5th Cir. Tex. 1999) -- Plaintiff moved to enjoin defendant corporation from selling and distributing software programs entitled "Quicken Family Lawyer." The district court granted the motion. The court vacated the injunction and judgment. The state legislature, subsequent to the filing of defendant's appeal, had enacted an amendment to Tex. Govt. Code Ann. § 81.101 (1998). The amendment, H.R. 1507, 76th Leg., Reg. Sess. (Tex. 1999), stated that the practice of law did not include the sale or distribution of computer software if the products stated clearly and conspicuously that the products were not a substitute for the advice of an attorney.
17. “Internet Merchant Service Agreements” September 2001 E-Commerce Supplement American Law Media http://www.bicklaw.com/Publications/Merchant_Service_Agreements.htm
18. "Internet Ticket Sales "New Jersey Law Journal November 14, 2005; http://www.bicklaw.com/Publications/E-tickets.htm
19. “Applying Technology to the Business of Health Care” New Jersey Law Journal April 30, 2012 http://www.bicklaw.com/Publications/E-BusinessofHealthcare.htm
Review Text Topics … Chapters 91 –100 91. Image (IMG) links normally increase legal liability 92. Offering securities through the Internet has legal limitations 93. E-notices help protect copyrights 94. Internet publicity releases help to limit legal liability 95. E-content writer's contract may be a work-for-hire agreement 96. Internet employment services agreements usually protects one party 97. Securities brokers' obligations apply to clients' Internet trading
98. Web Trust seal providers are liable to the public 99. Obscenity and indecency e-content regulation on the Internet is in flux 100. Some public access to the Internet is legally limited
XI November 2 International Law
1. "International Internet Law Suffers Growing Pains" New Jersey Law Journal January 6, 2015; http://bicklaw.com/Publications/E-growningpains.htm
2. "Integrating Trans-Atlantic Internet Medical Law" New Jersey Law Journal February 4, 2013; http://www.bicklaw.com/Publications/IntegratingTrans-AtlanticInternetMedicalLaw.htm
3. Protecting Domestic E-Commerce" May 31, 2010 New Jersey Law Journal http://www.bicklaw.com/Publications/e-import.htm
4. "Overseas Courts Limit American Internet Speech" New Jersey Law Journal July 3, 2006; http://www.bicklaw.com/Publications/OverseasCourtsLimitAmericanE-Speech.htm
5. Course Materials 4 - Overseas Attorney View of E-Speech Restrictions -- response to "Overseas Courts Limit American Internet Speech" New Jersey Law Journal July 3, 2006;
6. Export Controls
The international transfer of information from one nation to raises the issue of prohibiting such information to certain countries to achieve national goals. Most frequently, the objective of export regulation is to protect national military security. Export controls are most readily defensible when there is a clear relationship between the high technology product and military applications. Because Internet technology can often be used for military purposes, said transfer raises national security issues. Export Administration Act of 1979 - broadest application. The Act is administered through the Export Administration Regulations (EAR) by the Bureau of Export Administration (BXA) within the Commerce Department. These regulations govern the vast majority of dual-use high technology equipment.
7. Import Controls
8. Europe / Asia / America
9. "The Internet and Immigration" New Jersey Law Journal June 27, 2011; http://www.bicklaw.com/Publications/e-Immigration.htmReview
Text Topics … Chapter 101.Taxes apply to Internet transactions
Schedule second feedback meetings
XII November 9 Regulated activity - Gambling, Spam, and Drugs
1. "Internet Changes Medication Sales Regulations" Internet Law and Strategy Journal Volume 32, Number 5 February 2015 http://www.bicklaw.com/Publications/InternetChangesMedicationSalesRegulations.htm
2. "Selling Municipal Securities via the Internet" New Jersey Law Journal November 11, 2013; http://bicklaw.com/SellingMunicipalSecuritiesviatheInternet.htm
3. "Dual Use Spam" New Jersey Law Journal May 8, 2006; http://www.bicklaw.com/Publications/DualUseSpam.htm
4. Spammers Should Know Their Source New Jersey Law Journal April 11, 2005 http://www.bicklaw.com/SpamTargetSource.htm
5. Is your Client a Spammer? New Jersey Law Journal October 18, 2004 http://www.bicklaw.com/Publications/client_a_spammer.htm
6. Franchise Law Applies to Internet New Jersey Law Journal September 20, 2004 http://www.bicklaw.com/Publications/Franchise_Law.htm
7. Legality of Internet Wine Sales in Flux New Jersey Law Journal July 19, 2004 http://www.bicklaw.com/Publications/Legality_internet_sales.htm
8. Granholm v. Heald, 125 S. Ct. 1885 (U.S., 2005) -- State laws allowed in-state wineries to make direct sales to customers. They force out-of-state wineries to make sales only through wholesalers and retailers at greater expense. The wineries contended that the regulatory schemes discriminated against interstate commerce. States argued that the schemes were necessary to prevent underage persons from purchasing wine and to promote the collection of taxes. The Court held that the state laws discriminated against interstate commerce. It also found that the discrimination was not authorized by U.S. Const. amend XXI, § 2.
9 e-Credit Card Contract The Internet Newsletter November 2001 volume 6, Number 8 American Lawyer Media http://www.bicklaw.com/Publications/e-credit.htm
10. Purchase of Medications Online is Lawful New Jersey Law Journal April 9, 2004 http://www.bicklaw.com/Publications/medications_purchase_online.htm
11. E-Commerce Insurance New Jersey Law Journal August 19, 2002 http://www.bicklaw.com/Publications/e-commerce_insurance.htm
12. E-Outsourcing New Jersey Law Journal October 29, 2001 http://www.bicklaw.com/Publications/e-outsourcing.htm
13. Funding e-Firms The Daily Deal October 23, 2001 http://www.bicklaw.com/Publications/funding%20e-firms.htm
XIII November 16 Student Presentations and special topics
Special topics and begin Class Presentations of Guided Research (10 minutes each) … peer critique
1. Litigating Workplace Injuries in a Virtual Office" New Jersey Law Journal October 28, 2014 http://www.bicklaw.com/E-workplace.htm
2. "Applying Technology to the Business of Health Care" New Jersey Law Journal April 30, 2012; http://www.bicklaw.com/Publications/E-BusinessofHealthcare.htm
3. Matrimonial Lawyers Have a New Tool New Jersey Law Journal January 3, 2005 http://www.bicklaw.com/Publications/e-MatrimonialLaw.htm
4. RIAA Suits The Internet Newsletter September 26, 2003 http://www.bicklaw.com/Publications/RIAA_Suits.htm
5. The Recording Industry Association of America Sues Its Members' Customers New Jersey Law Journal November 3, 2003 http://www.bicklaw.com/Publications/E-download_suits.htm
6. Internet Charity Registration Requirements New Jersey Law Journal May 9, 2005 http://www.bicklaw.com/InternetCharityRules.htm
NO CLASS NOVEMBER 23rd---- Thanksgiving recess
XIV Final Class --- November 30 --- Student Presentations and special topics Special topics and begin Class Presentations of Guided Research (10 minutes each) … peer critique
Work product due (including: research logs, outlines, due in class, summary of meetings, draft of final work product, presentation notes / peer review comments and final work product)